Security DevOps Maturity Model (SDOMM)
This blog post covers my talks about Security DevOps in general and a maturity model to define steps in reaching more automation of certain security checks. The main idea is to define a roadmap of how projects can reach a level of automation (preferably with OpenSource tools) to check for certain security aspects during the CI (Continuous Integration) build chain.
This first part covers my talk at the OWASP AppSecEU 2015 conference held last week in Amsterdam. I had the chance to present best practices of how OpenSource tools (used in the DevOps and security communities) can be properly chained together to form a framework that can - as part of an agile software development CI chain - perform automated checking of certain security aspects. This does not remove the requirement for manual pentests, but tries to automate early security feedback to developers. My talk introduced a SecDevOps Maturity Model (SDOMM) of different stages of automated security testing and presented concrete examples of how to achieve each stage with open source security tools.
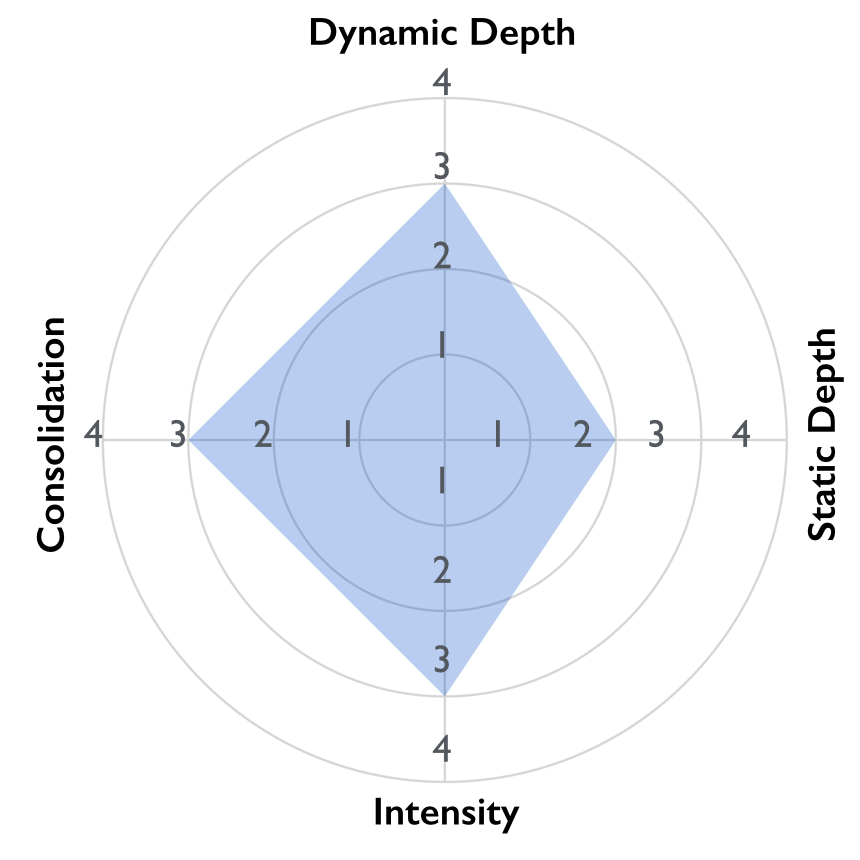
The four axes of SDOMM
In my talk at AppSecEU 2015 I introduced the following four axes of the Security DevOps maturity model and presented ways to reach these with OpenSource tools:
- Dynamic Depth:
How deep are dynamic scans executed within a Security DevOps CI chain? - Static Depth:
How deep is static code analysis performed within a Security DevOps CI chain? - Intensity:
How intense are the majority of the executed attacks within a Security DevOps CI chain? - Consolidation:
How complete is the process of handling findings within a Security DevOps CI chain?
Videos & Slides
As the session was recorded by the great conference supporting team, a video will be published soon via the OWASP youtube channel - along with the slides. Meanwhile you can access the PDF slidedeck directly here. Watch out for updates of this article as soon as the video is available.