Closing the AI agent identity governance gap
AI agents are a rapidly growing class of non-human identities, yet most IAM programs still treat them like ordinary service accounts.
As a speaker with international conference experience (Black Hat Arsenal USA, DEF CON AppSec Village USA, RSA Conference USA, Oracle JavaOne, Black Hat Arsenal Europe, Black Hat Arsenal Asia, DeepSec, BruCON, Troopers, MCTTP, OWASP AppSecEU, OWASP AppSec Days, DevOpsCon, JAX, Heise devSec, Heise Sec-IT, Heise Herbstcampus, RuhrSec, JCon, JavaLand, Internet Security Days, IT-Tage Frankfurt, OOP, and others) I’m definitely enjoying to speak, present keynotes, and train about IT-Security topics.

Deep penetration testing of web applications and APIs — including business logic flaws and chained attack paths.

Security review of Kubernetes and OpenShift platforms covering RBAC, pod security, container images, and benchmark compliance.

Cloud security audit combining hardening with pentesting experience to improve the security posture in your AWS, Azure, or GCP setup.

AI agents are a rapidly growing class of non-human identities, yet most IAM programs still treat them like ordinary service accounts.
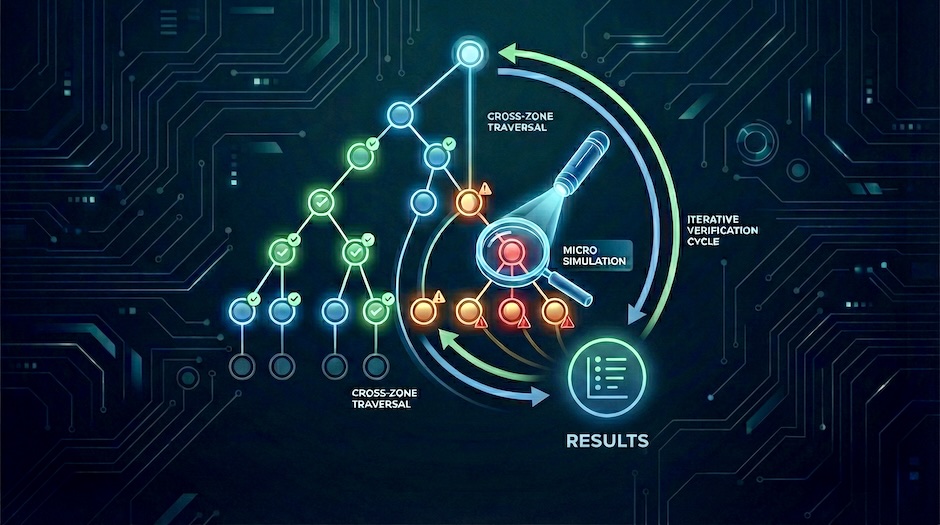
Move agentic AI threat models from assumptions to tested control assertions using attack-tree-driven micro simulations.

How attackers bypass text-based guardrails by embedding malicious instructions in images and audio, and the layered defenses required to counter them.